The file extensions ransomware is targeting certain clusters of file formats :
- Commonly used office file extensions (.ppt, .doc, .docx, .xlsx, .sxi).
- Less common and nation-specific office formats (.sxw, .odt, .hwp).
- Archives, media files (.zip, .rar, .tar, .bz2, .mp4, .mkv)
- Emails and email databases (.eml, .msg, .ost, .pst, .edb).
- Database files (.sql, .accdb, .mdb, .dbf, .odb, .myd).
- Developers’ sourcecode and project files (.php, .java, .cpp, .pas, .asm).
- Encryption keys and certificates (.key, .pfx, .pem, .p12, .csr, .gpg, .aes).
- Graphic designers, artists and photographers files (.vsd, .odg, .raw, .nef, .svg, .psd).
- Virtual machine files (.vmx, .vmdk, .vdi).
Indicators of compromise (IoC):
- Ransomware is writing itself into a random character folder in the 'ProgramData' folder with the file name of "tasksche.exe" or in 'C:\Windows\' folder with the filename "mssecsvc.exe" and "tasksche.exe".
- Ransomware is granting full access to all files by using the command:
- Icacls . /grant Everyone:F /T /C /Q
- Using a batch script in the video's description for operations
Please find the video explanation here
Reversion stuff (How application works):
Step 1: The malware contains the hardcoded password “WNcry@2017”

Step 2: The malware drops a encrypted zip file from a source named “XIA”

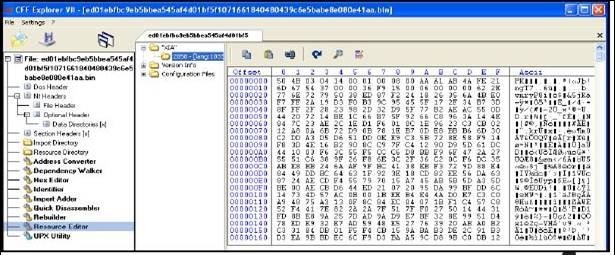
Step 3: Extract the resource with the help of CFF Explorer
Step 4: Open the exe file with WinZip or WinRAR you will get below files

Step 5: Unzip the file name s.wnry

Step 6: Wanadecryptor process starts here

Countermeasure for avoid ransomware:
Patch:
- If you want to stay safe from this, patching is really one option
- The patch has been available since march
- . If you can’t patch (If you are on windows server 2003),Consider network segmentation
Network Segmentation:
- Restrict port 445 traffic to where it is absolutely needed using router ACLs
- Use private VLANs if your edge switches support this feature
- Use host based firewalls to limit communication on TCP 445,especially between workstations.
Microsoft Update:
· Apply patches to windows systems as mentioned in Microsoft Security Bulletin MS17-010
https://technet.microsoft.com/library/security/MS17-010
· Microsoft patch for unsupported versions such as windows XP,Vista,Server 2003,Server 2008 etc.
http://www.catalog.update.microsoft.com/Search.aspx?q=KB4012598
· To prevent data loss Users @ Organizations are advised to take backup of critical data
· Block SMB ports on Enterprise Edge/perimeter network devices [UDP 137,138, and TCP 139,445] or Disable SMBv1
https://support.microsoft.com/en-us/help/2696547
For Users:
- Deploy antivirus protection
- Block all the spams
- Perform regular backups of all information’s and it should stored offline
- Don’t open any attachments from email
- Disable macros in Microsoft office products
For Organizations:
- Establish a Sender Policy Framework (SPF),Domain Message Authentication Reporting and Conformance (DMARC), and DomainKeys Identified Mail (DKIM) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Deploy Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA%, %PROGRAMDATA% and %TEMP% paths. Ransomware sample drops and executes generally from these locations. Enforce application whitelisting on all endpoint workstations.
- Deploy web and email filters on the network. Configure these devices to scan for known bad domains, sources, and addresses; block these before receiving and downloading messages. Scan all emails, attachments, and downloads both on the host and at the mail gateway with a reputable antivirus solution.

